On August 15, 2012, Saudi Aramco discovered that 35,000 of its computers had been wiped by the Shamoon malware — replacing every hard drive's master boot record with the image of a burning American flag. The company purchased 50,000 replacement hard drives and took nearly five months to fully restore operations (CNN Money, 2015). The technology existed. The preparedness did not. Fourteen years later, this pattern still repeats across the GCC.
For decades, Disaster Recovery meant a secondary data center, backup tapes, and a binder of printed procedures. That model assumed disasters were rare and predictable — a server room fire, a localized hardware failure. Organizations treated continuity planning as an annual compliance exercise.
That world no longer exists. The IBM Cost of a Data Breach Report 2024 found that organizations take an average of 258 days to identify and contain a breach, with the average cost of a ransomware attack reaching USD 4.91 million. Mandiant's M-Trends 2024 Special Report (Google Cloud) puts the global median attacker dwell time at 10 days — meaning adversaries operate inside your environment for over a week before detection.
Against these realities, a 48-hour Recovery Time Objective is not a safety net — it is an existential risk. Ransomware-as-a-service attacks can encrypt an entire enterprise environment in under four hours. Cascading cloud-provider outages can disable SaaS tools relied upon by thousands of employees. Regulatory shifts can invalidate data-hosting arrangements overnight.
“Everything fails, all the time. The question is not whether you will face a failure — it is whether your architecture is designed to handle it gracefully when it happens.”
Werner Vogels, CTO, Amazon Web Services (AWS re:Invent 2024 Keynote)
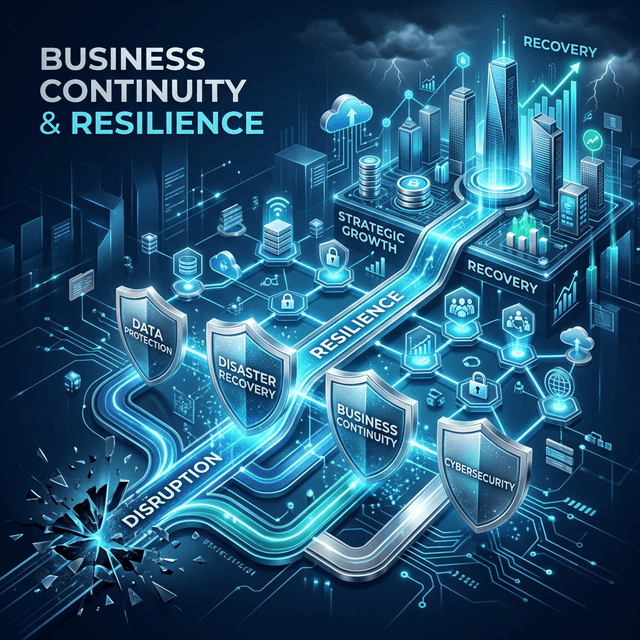
Leading enterprises that have modernized their continuity posture share a common architecture built on four pillars that go far beyond "backup and restore":
Modern continuity begins months or years before failure. AI-powered threat monitoring platforms continuously scan for warning signs across your digital environment — identifying suspicious activity, emerging vulnerabilities, and unusual patterns before they escalate into full-blown incidents. The business case is clear: Mandiant's 2024 data shows that organizations with internal detection capabilities identified threats in a median of 5 days, compared to 26 days when the notification came from an external party. That 21-day gap is the difference between a contained incident and a front-page crisis.
Emirates NBD, one of the largest banking groups in the Middle East, partnered with McKinsey to deploy AI-driven analytics across its operations — building a bankwide data lake as the foundation for continuous risk intelligence and real-time anomaly detection (McKinsey, "How a UAE bank transformed to lead with AI and advanced analytics").
The single biggest failure mode in traditional DR is human latency. When an incident hits at 2:30 AM on a Friday, the chain of phone calls and manual procedures introduces hours of delay. Modern resilience platforms replace printed checklists with automated, pre-tested response playbooks. When a threat is detected, the system autonomously contains the affected area, activates backup systems, notifies the incident team, and maintains a complete audit trail — all within minutes rather than hours. Human expertise is applied to strategic decisions, not repetitive manual procedures.
If your backup systems use the same access credentials as your primary environment, a single compromised account can encrypt both simultaneously — rendering your backups useless exactly when you need them. The modern standard requires immutable backups: once data is written, it cannot be modified or deleted for a defined retention period, even by an administrator. This is complemented by isolated recovery environments — separate infrastructure that validates your backups without exposing them to the same risks as your production systems.
The financial case is stark: the Sophos State of Ransomware 2024 report found average recovery costs (excluding ransom payments) reached USD 2.73 million, with average ransom payments hitting USD 2 million. Immutable storage eliminates the ransom leverage entirely.
Technical recovery is half the battle. A well-prepared Business Continuity Plan includes pre-drafted communication matrices — customer notifications, regulatory disclosures (SAMA, NDMO in Saudi Arabia; CBUAE in the UAE), media statements, and internal all-hands messaging — activatable within minutes of an incident declaration. According to Harvard Business Review, 78% of consumers said they would continue to support a brand that communicated openly during a crisis. GCC regulators increasingly mandate specific disclosure timelines, making this an operational and compliance requirement.
A structured Resilience Maturity Assessment should cover five domains: Detection and Intelligence, Protection Architecture, Response Automation, Recovery Validation, and Communication Readiness. Most organizations find significant gaps in at least three of these five. Here are the highest-leverage first moves:
Need help building a resilience strategy for your organization? Bridges designs and implements disaster recovery and business continuity solutions for GCC enterprises. Book a free consultation →
Bridges Development Studio
Digital Resilience Practice
Covering technical and strategic shifts across the Middle East. Deep-diving into AI transformation, regional regulatory changes, and digital infrastructure developments impacting major enterprises in the GCC.
More insights into digital transformation.